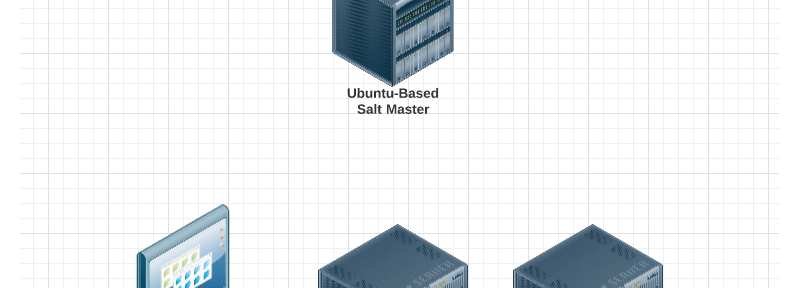
This how-to on Windows Salt minions will just scratch the surface of the power behind Salt, and will cover remote execution, installation and management. Please note: I’m new to Salt, and I’m a recovering Windows syasdamin from the 2000-2013 era. This means I probably have a bunch of out-moded ways of working with Windows. To …
Continue reading “Getting Started with Salt Stack Windows Minions”